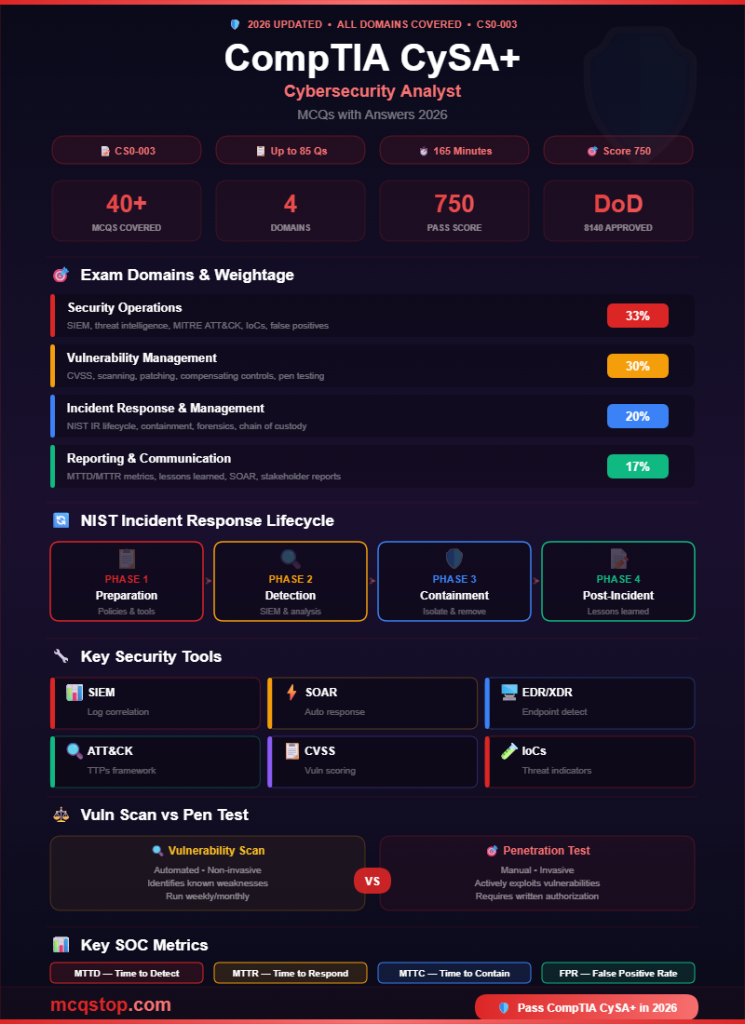
Security Operations
Domain 1 — 33% of Exam (Highest Weight)
Question 01
Which security tool aggregates and correlates log data from multiple sources across an organization to detect security threats in real time?
ASIEM (Security Information and Event Management) ✅
BIDS (Intrusion Detection System)
CDLP (Data Loss Prevention)
DWAF (Web Application Firewall)
💡 Explanation: A SIEM (Security Information and Event Management) collects, normalizes, and correlates log data from firewalls, servers, endpoints, applications, and network devices to detect anomalies and security incidents. Popular SIEMs include Splunk, Microsoft Sentinel, IBM QRadar, and Elastic SIEM. SIEM is the backbone of a Security Operations Center (SOC). IDS detects intrusions on a single network. DLP prevents data exfiltration. WAF protects web applications.
Question 02
A SOC analyst notices that a SIEM alert was generated, but after investigation, determines the activity was legitimate and not a real threat. What is this called?
AFalse positive ✅
BFalse negative
CTrue positive
DTrue negative
💡 Explanation: False positive = alert triggered but no real threat (benign activity flagged as malicious). False negative = real threat missed (attack not detected). True positive = real threat correctly detected. True negative = benign activity correctly ignored. SOC analysts spend significant time triaging false positives. Reducing false positives through SIEM tuning is a critical CySA+ skill.
Question 03
Which threat intelligence framework, developed by MITRE, provides a knowledge base of adversary tactics, techniques, and procedures (TTPs) used in real-world cyberattacks?
AMITRE ATT&CK ✅
BNIST Cybersecurity Framework
CISO 27001
DOWASP Top 10
💡 Explanation: MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) is a globally-accessible knowledge base that catalogs how attackers operate. It organizes TTPs into a matrix of tactics (Initial Access, Execution, Persistence, etc.) and techniques. SOC teams use ATT&CK to map detected behaviors to known attack patterns. NIST CSF is a risk management framework. ISO 27001 is a security management standard. OWASP focuses on web app vulnerabilities.
Question 04
Which type of threat intelligence includes specific indicators like malicious IP addresses, domain names, file hashes, and URLs that can be directly fed into security tools?
AStrategic threat intelligence
BTactical threat intelligence (Indicators of Compromise — IoCs) ✅
COperational threat intelligence
DPolitical threat intelligence
💡 Explanation: Tactical intelligence includes specific, actionable Indicators of Compromise (IoCs) — malicious IPs, domains, file hashes (MD5/SHA256), email addresses, and URLs. These can be loaded into SIEM rules, firewall blocklists, and endpoint detection tools. Strategic intelligence is high-level (trends, motivations — for executives). Operational intelligence provides details about specific attacks (who, when, how). Know all three levels for CySA+.
2
Vulnerability Management
Domain 2 — 30% of Exam
Question 05
Which scoring system rates the severity of software vulnerabilities on a scale of 0.0 to 10.0, with 10.0 being the most critical?
ACVSS (Common Vulnerability Scoring System) ✅
BCVE (Common Vulnerabilities and Exposures)
CCWE (Common Weakness Enumeration)
DNVD (National Vulnerability Database)
💡 Explanation: CVSS provides a numerical severity rating (0.0–10.0): None (0.0), Low (0.1–3.9), Medium (4.0–6.9), High (7.0–8.9), Critical (9.0–10.0). It considers attack vector, complexity, privileges required, user interaction, and impact on confidentiality/integrity/availability. CVE is a unique identifier for vulnerabilities (e.g., CVE-2024-1234). CWE categorizes software weakness types. NVD is NIST’s database of CVEs with CVSS scores.
Question 06
A vulnerability scan identifies a critical vulnerability on a production web server. The patch is available but requires a reboot during business hours. What should the analyst recommend FIRST?
AImmediately apply the patch regardless of downtime
BApply a compensating control (WAF rule, network segmentation) while scheduling the patch during a maintenance window ✅
CIgnore the vulnerability since it requires downtime
DRemove the web server from the network permanently
💡 Explanation: When a patch can’t be applied immediately, implement compensating controls to mitigate risk while scheduling the permanent fix. Compensating controls include: WAF rules, network segmentation, IPS signatures, disabling vulnerable features, or restricting access. Then apply the patch during a planned maintenance window. Never ignore critical vulnerabilities, and never cause unplanned outages without authorization. This balanced approach is what CySA+ tests.
Question 07
What is the difference between a vulnerability scan and a penetration test?
AThey are the same thing
BA vulnerability scan identifies known weaknesses; a penetration test actively exploits them to determine real-world impact ✅
CA penetration test is automated; a vulnerability scan is manual
DVulnerability scans are more invasive than penetration tests
💡 Explanation: Vulnerability scans are automated, non-invasive assessments that identify known vulnerabilities (missing patches, misconfigurations). Tools include Nessus, Qualys, and OpenVAS. Penetration tests are manual, authorized simulations where ethical hackers actively exploit vulnerabilities to assess real-world impact. Pen tests are more invasive and require explicit written authorization (Rules of Engagement). Scans are run frequently; pen tests are done periodically.
Question 08
Which type of vulnerability scan uses credentials to log into systems and provides more accurate and comprehensive results by checking internal configurations?
ANon-credentialed (unauthenticated) scan
BCredentialed (authenticated) scan ✅
CPassive scan
DExternal scan
💡 Explanation: Credentialed scans log into the target system using valid credentials, enabling deep inspection of installed software versions, registry settings, file permissions, and internal configurations. This produces far fewer false positives and identifies more vulnerabilities. Non-credentialed scans only see what’s externally visible (like an attacker would). Passive scans monitor network traffic without sending packets. Always prefer credentialed scans for accuracy.
3
Incident Response & Management
Domain 3 — 20% of Exam
Question 09
According to the NIST Incident Response lifecycle, what are the four phases of incident response in the correct order?
APreparation → Detection & Analysis → Containment, Eradication & Recovery → Post-Incident Activity ✅
BDetection → Containment → Preparation → Recovery
CAnalysis → Response → Remediation → Reporting
DIdentification → Notification → Investigation → Closure
💡 Explanation: NIST SP 800-61 defines four IR phases: (1) Preparation — policies, tools, training, communication plans; (2) Detection & Analysis — identify and investigate incidents using SIEM, logs, alerts; (3) Containment, Eradication & Recovery — isolate the threat, remove it, restore systems; (4) Post-Incident Activity — lessons learned, update procedures, documentation. This lifecycle is circular — post-incident improvements feed back into preparation.
Question 10
A compromised server has been identified in the network. What is the FIRST step the incident response team should take?
AWipe and reimage the server
BContain the threat by isolating the server from the network ✅
CNotify the CEO immediately
DRun an antivirus scan on all other servers
💡 Explanation: Containment is the first priority once a compromised system is identified — isolate it from the network to prevent lateral movement and further damage. Do NOT wipe the server first, as this destroys forensic evidence. Containment strategies include: network isolation (disconnect/VLAN), disabling accounts, blocking IPs at the firewall, or using endpoint detection to quarantine. After containment, proceed to eradication and recovery.
Question 11
During a forensic investigation, an analyst needs to create an exact bit-for-bit copy of a hard drive while preserving the original evidence. What should they create?
ABackup copy
BForensic image (disk image) ✅
CVM snapshot
DFile system copy
💡 Explanation: A forensic image (disk image) is a bit-for-bit exact copy of the entire drive, including deleted files, slack space, and unallocated space. Tools: FTK Imager, dd, EnCase. The image is verified using cryptographic hash values (MD5/SHA-256) to prove integrity. Analysts work on the image copy, never the original. Chain of custody must be maintained throughout. This is essential for legal admissibility of evidence.
4
Reporting & Communication
Domain 4 — 17% of Exam
Question 12
Which metric measures the average time it takes an organization to detect a security incident from the moment it occurs?
AMTTD (Mean Time to Detect) ✅
BMTTR (Mean Time to Respond)
CMTBF (Mean Time Between Failures)
DRPO (Recovery Point Objective)
💡 Explanation: MTTD measures how quickly threats are discovered — lower is better. MTTR (Mean Time to Respond/Remediate) measures how quickly the team responds and resolves incidents. MTTC (Mean Time to Contain) measures containment speed. These SOC metrics are reported to management to demonstrate security posture improvement. Industry average MTTD for breaches is ~200 days — the goal is to reduce this significantly.
Question 13
After resolving a major security incident, the incident response team conducts a meeting to review what happened, what went well, and what can be improved. What is this meeting called?
ALessons learned / Post-incident review ✅
BRisk assessment
CVulnerability scan
DPenetration test
💡 Explanation: The lessons learned (post-incident review / after-action report) is the final phase of incident response. It should occur within 1-2 weeks of the incident and include: what happened, timeline of events, what worked well, what failed, root cause analysis, and recommended improvements. Findings should be documented and fed back into the incident response plan, security policies, and training programs.
Question 14
Which security solution combines SIEM capabilities with automated incident response, orchestration, and threat intelligence into a single platform?
AEDR (Endpoint Detection and Response)
BSOAR (Security Orchestration, Automation, and Response) ✅
CNAC (Network Access Control)
DPAM (Privileged Access Management)
💡 Explanation: SOAR platforms automate repetitive SOC tasks — like blocking IPs, quarantining endpoints, and enriching alerts with threat intelligence — through pre-built playbooks. SOAR integrates with SIEM, firewalls, EDR, and ticketing systems. Popular SOAR tools: Splunk SOAR, Palo Alto XSOAR, IBM Resilient. EDR monitors endpoints specifically. NAC controls network access. PAM manages privileged accounts. SOAR is a key CySA+ concept.





Leave a Comment